
Every AI agent in your organization connects to the outside world through MCP servers. FireTail discovers every one of them sanctioned or not and governs what they can do.

FireTail surfaces every MCP server active in your environment by consolidating three discovery tiers into a single dashboard: Code, Cloud, and Endpoint. If an MCP server is connecting to an AI agent anywhere in your stack, FireTail finds it, including the local deployments your developers never told IT about.
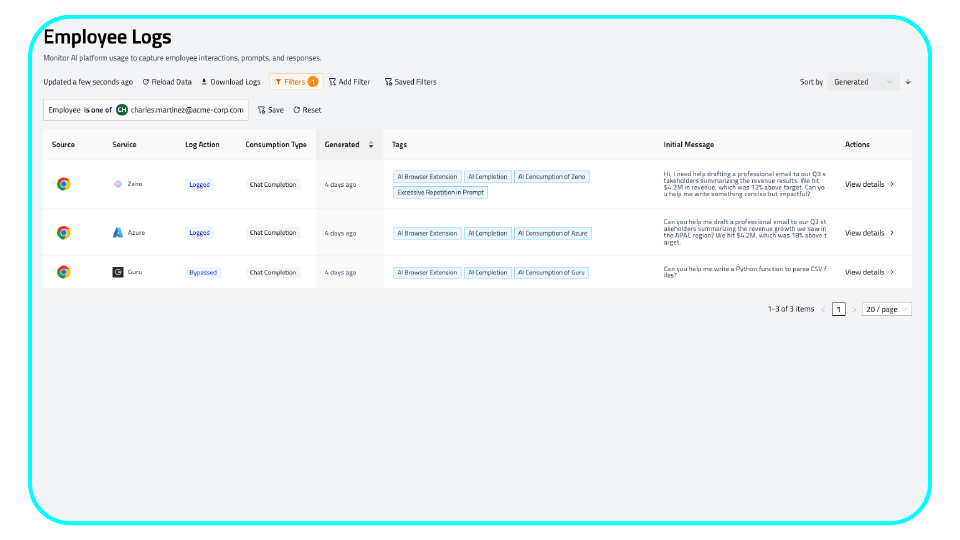
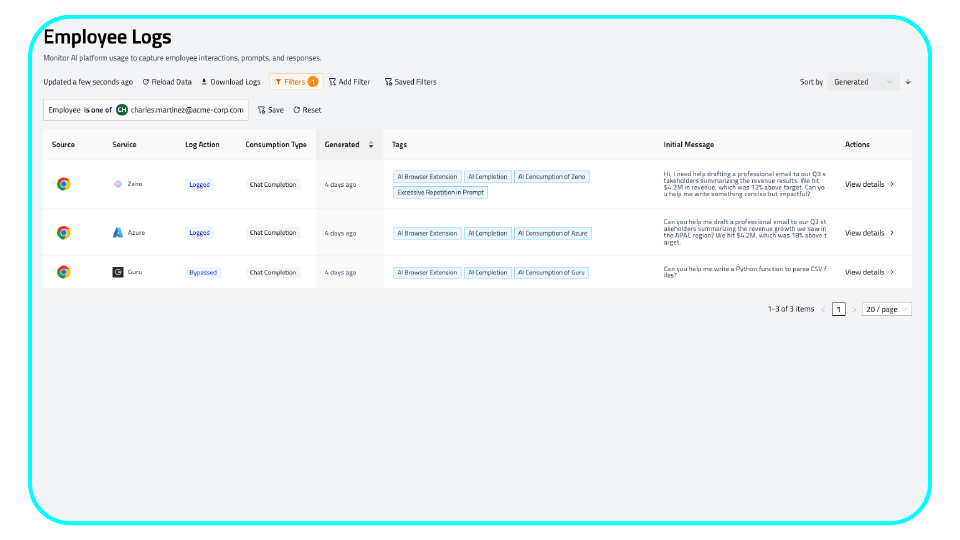
Maintain a unified audit trail of every MCP tool call, agent invocation, and data transfer across your entire AI stack. Capture what was called, by which agent, with what parameters, and what data was returned, giving your security team the full context needed to detect anomalies and respond fast.
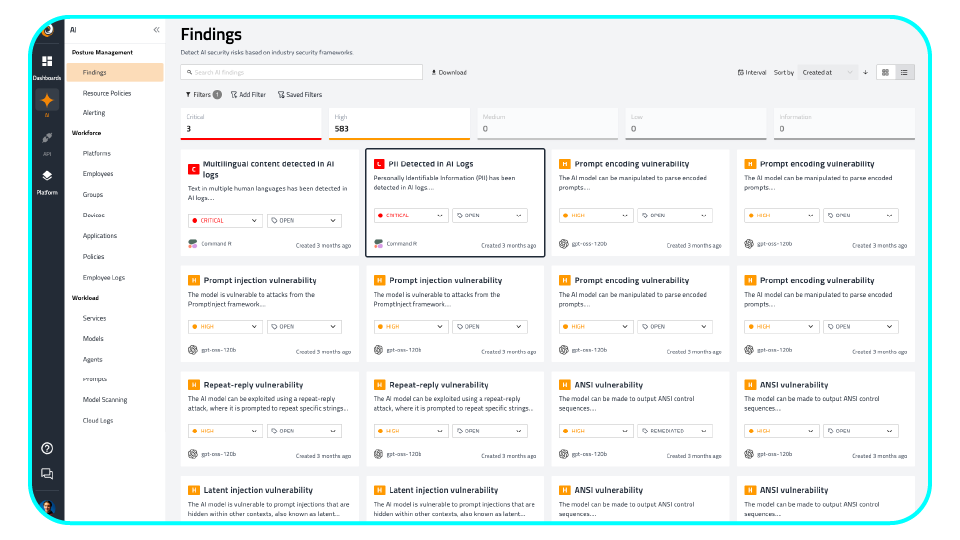
Automatically surface and prioritize high-stakes MCP risks including PII leakage through tool-calling, exposed API secrets, and shadow MCP server connections. FireTail findings are enriched with full behavioral context so your team spends time remediating real threats, not chasing noise.
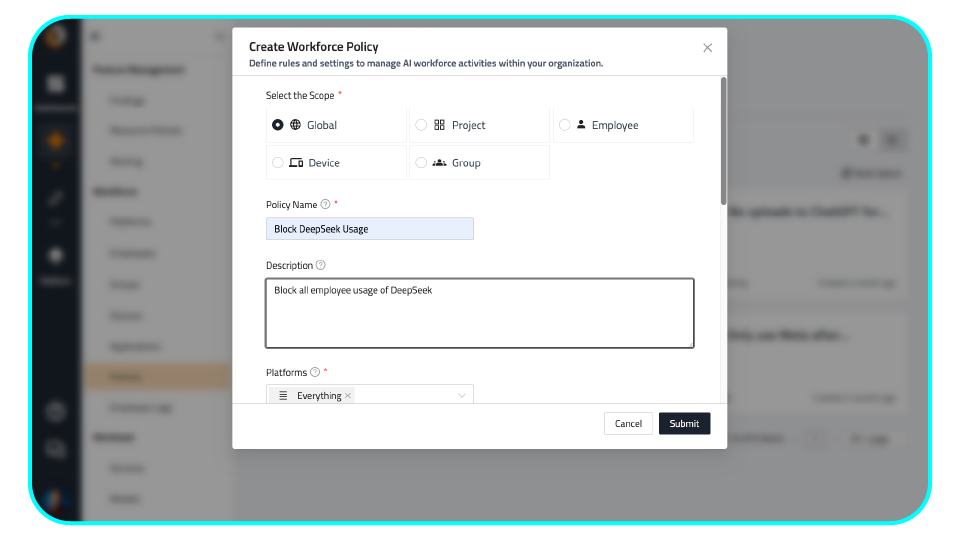
Enforce granular policies that define exactly which MCP servers are sanctioned, what tools they can expose, and which AI clients are permitted to connect. Set rules at the global, team, or individual agent level to ensure every MCP connection operates within your approved governance boundaries.
Discover MCP servers across code repositories, cloud environments, and developer endpoints, including shadow deployments that traditional security tools completely miss.
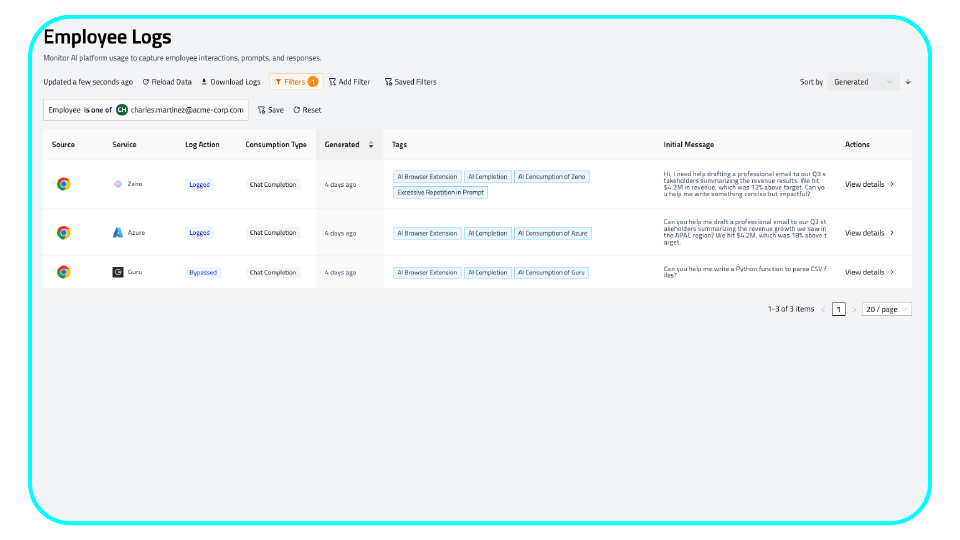
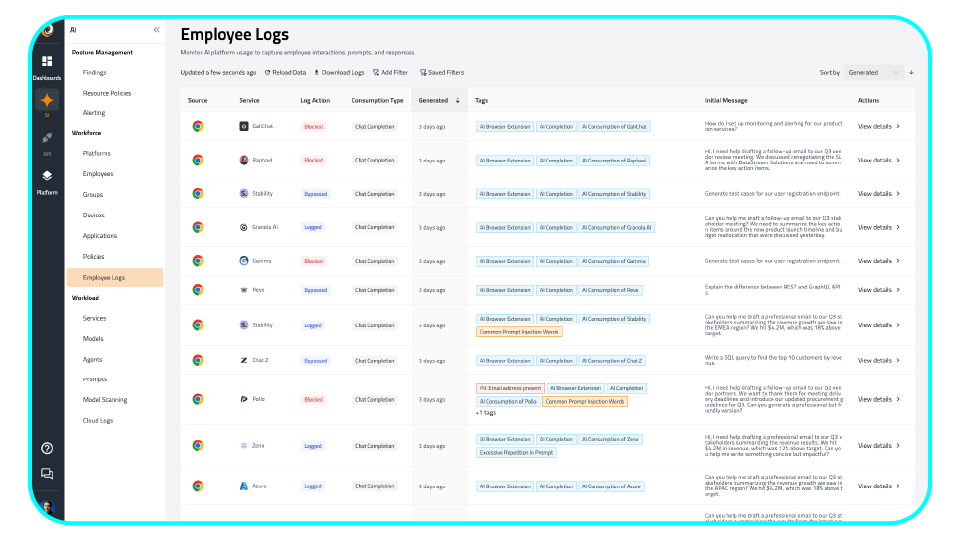
Monitor every MCP tool call as it happens. Detect anomalous patterns, sudden traffic spikes, and data exfiltration attempts before they become incidents.
FireTail maps directly to OWASP Agentic Top 10 ASI04 (Supply Chain Compromise) and NIST AI RMF. Get audit-ready compliance reporting from day one, with no manual mapping required.
Get complete MCP visibility across your environment in under 15 minutes. No agents required for cloud and code scanning, with zero friction deployment for security teams under pressure.
Security Architect @ Global Financial Services Firm
Schedule Your Demo
Use FireTail's continuous discovery to maintain a live, accurate registry of every MCP server in your environment, complete with connection history, exposed tools, and data source access. Know exactly what your AI is connecting to, always.
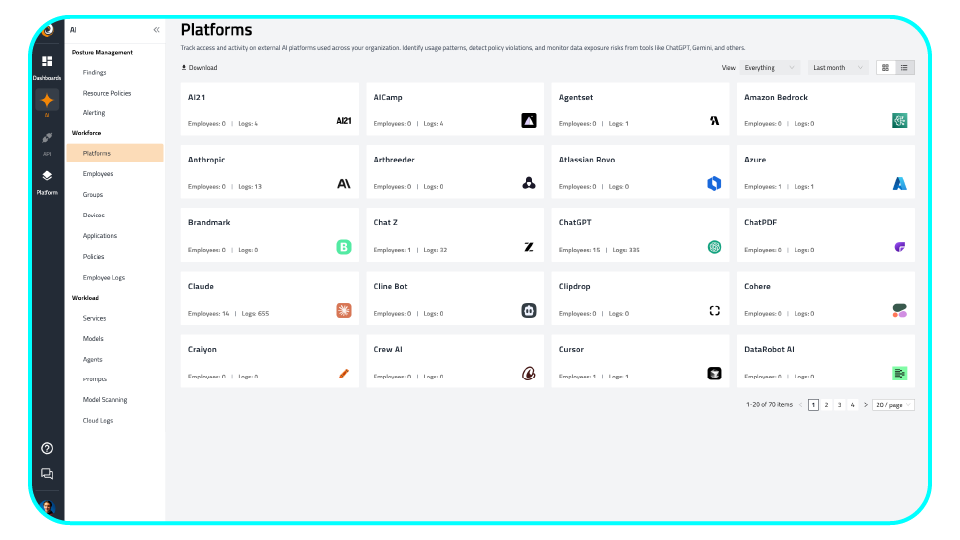
Surface the MCP servers with the broadest access, the weakest authentication, and the highest tool-call volume. FireTail risk-scores every server in your inventory so your team always knows where to focus first.
Generate on-demand audit reports aligned to OWASP Agentic Top 10, NIST AI RMF, and MITRE ATLAS. When your board or auditors ask how you are managing MCP risk, FireTail gives you the evidence in seconds.
Find answers to common questions about protecting your MCP infrastructure with FireTail.
MCP server security is the practice of discovering, monitoring, and governing the Model Context Protocol servers that connect AI agents to enterprise tools, data, and services. FireTail provides the visibility and governance layer needed to manage this high-privilege, often unmonitored attack surface before it becomes a breach.
FireTail scans simultaneously across code repositories, cloud infrastructure, and developer endpoints. We surface every MCP server active in your environment, including locally deployed servers running inside developer IDEs and automation tools, ensuring no connection between an AI client and enterprise systems goes unmonitored.
Prioritize RCE via tool-calling (CVE-2025-6514, CVSS 9.6), SSRF vulnerabilities affecting approximately 36.7% of MCP servers in the wild, and supply chain tool poisoning. FireTail maps every discovered server against known CVEs and behavioral anomalies so your team can remediate the highest-risk threats first.
Yes. FireTail maps directly to OWASP Agentic Top 10 ASI04 (Supply Chain Compromise) and ASI02 (Tool Misuse), as well as NIST AI RMF governance requirements. Security teams receive audit-ready compliance reporting from day one with no manual mapping required.